
Heather Zeiger

We’re Slowly Learning About China’s Extensive Hacking Network
China’s state-backed hackers have embedded malware within U.S. programs used to manage clean drinking water, the power grid, and air traffic, among others
China, Cybertheft, and the Ethics of Espionage
All nations spy, but espionage crosses a moral line when it costs normal civilians their jobs.
Spies and Lies: China’s Cyberespionage Is on an Unprecedented Level
Chinese cybertheft is an ever-increasing threat.
COVID Helped China Get Ahead on Genetic Therapies
Why is China trying to lead the world in genetic technology?
China’s Chatbot Toes the Party Line
How will China control what AI does and doesn't say?
The Chinese Spy Balloon Saga, Part 2
China continues to deny that the balloon was used for spying on military basesThe U.S. has shot down four aerial objects this month, one of which was a Chinese surveillance balloon that had traversed the U.S. from Idaho to the Atlantic Ocean. Part 1 of Mind Matters Spy Balloon Saga provides an overview of the four aerial objects that were shot down. Since then, several media outlets found additional information on China’s global high-altitude balloon program, including that the balloon shot down in the Atlantic likely launched from Hainan Island and was intended to surveil U.S. Pacific military bases in Guam and Hawaii. The balloon inadvertently traversed into the continental U.S. Here is a rundown of what of several media outlets have reported: There are 2 known launch sites in China: Dorbod Banner Read More ›

The Chinese Spy Balloon Saga (Part 1)
China may be playing a psychological game with the United StatesOn February 4, the U.S. shot down a Chinese high-altitude surveillance balloon over the Atlantic Ocean off the coast of South Carolina. The balloon was first spotted on January 28 over the Aleutian Islands, and then traveled over Alaska, through Canada, and then into Idaho. Chinese spokespersons maintained that it was a meteorological research balloon that had veered off-course. However, recovery crews confirmed that the balloon platform was equipped with communication surveillance and interception tools. Since then, three other aerial objects, all flown within the vicinity of sensitive U.S. military sites, have been shot down. The other three are not confirmed to be of Chinese origin and have not been identified as surveillance balloons. NORAD (North American Aerospace Defense Command) Read More ›

Life After Zero-Covid: Protesters Are Rounded Up
The way Beijing lifted its zero-Covid measures was just as unethical as the zero-Covid measures themselvesIn response to widespread protests and a slumping economy, the Chinese Communist Party abruptly reversed its zero-Covid policies. Rather than taking responsibility for bad policy, however, Beijing instead left a scared and immunologically vulnerable populous to fend for itself in a country with an inadequate healthcare structure. Analysts have said that rather than using the lockdowns as an opportunity to fortify its healthcare system, which has been inadequate to serve China’s large population even before the coronavirus, Beijing doubled down on state and local surveillance. In the next couple of articles, we will look at the aftermath of Beijing’s zero-Covid policy, a policy that General Secretary Xi Jinping has used to justify the superiority of China’s socialist system over “chaotic” Read More ›
China: Protesters Evade Censors and Confront State Surveillance
Chinese citizens are known for their clever plays on words to evade social media censors.The graffiti on the bathroom wall at the university said there would be a gathering in honor of the people who had died in an apartment fire in Urumqi, Xinjiang. Bathrooms usually do not have surveillance cameras, so this announcement would probably go unnoticed by censors. It is better than risking punishment by posting on social media. In another city, Chinese citizens discretely shared information about the location of a vigil for the Urumqi victims on WeChat in the guise of dinner plans. A number of people died in the fire, whose toll was likely inflated because emergency vehicles were unable to access the building due to zero-Covid measures. Social media posts showed doors that were barred shut and barricades Read More ›

When the Chinese Had Had Enough, Their Government Had To Listen
Embarrassingly, Xi had already declared victory over the virus in 2020, touting authoritarian governments as better able to respond“The political object is the goal, war is the means of reaching it, and means can never be considered in isolation from their purpose.” (von Clausewitz, On War) Beijing’s zero-Covid policy was not sustainable. The highly publicized events in October and November in Urumqi, Xinjiang and at the Zhengzhou Foxconn factory served as the inciting events for what became a nationwide call for ending zero-Covid, giving people their freedoms — and there were even calls for Xi Jinping to step down. In the course of a week, Beijing went from touting zero-Covid to easing restrictions to censoring mentions of zero-Covid policy online. In November in Urumqi, the capital of Xinjiang, several residents, including four children, died in an apartment fire Read More ›

China: Massive Protests at Cell Phone Plant Continue
One accusation against Apple is that it has consistently failed to live up to its responsibilities as a global leader at the top of the supply chain.At the Foxconn plant in Zhengzhou where thousands of employees walked out on October 29, protests broke out on November 23. They were led by new hires staying on a campus dormitory after they learned that they would have to work an additional two months at lower pay before they receive their promised bonuses for coming to Foxconn to cover for the October exodus. Additionally, workers complained of inadequate food and fear of Covid exposure. Workers were offered 25,000 yuan (US$3,500) for two months of work, a 50% increase on the posted maximum wage. When they learned of changes in their agreement, employees at the dorm responded by pulling down outdoor tents (for Covid testing) and destroying a surveillance camera. Read More ›

China’s Foxconn Walkout: How Fear Messaging Can Backfire
Workers were caught in a conflict between unrealistic COVID Zero messaging from the government and seasonal performance demands from the employerAround this time of year, the factories that produce Apple’s iPhones hire thousands of additional workers to meet the demand for the holiday season. While Apple is an American company and the electronics are designed in-house, the manufacturing is done overseas where labor costs are cheaper. One of the largest manufacturers for Apple’s iPhone products is Hon Hai Technology Group, better known as Foxconn, a Taiwan-based company with factories in several countries, including mainland China. One of its largest facilities is in Zhengzhou, the capital of Henan province — dubbed “iPhone City” by the locals. Thus the Zhengzhou Foxconn factory was slated to make 80% of the iPhone 14 models and 85% of the iPhone Pro models before the end Read More ›

Lab Leak Theory: A Biohazard Was First Noted in 2019
The dispatches indicate a “grave and complex situation” prompting an emergency visit from the director of the Chinese Academy of SciencesA US Senate interim report has recently concluded that that “the Covid-19 pandemic was, more likely than not, the result of a research-related incident.” The 35-page report, prepared by the minority oversight staff of the of the Senate Committee on Health, Education, Labor, and Pensions (HELP), used publicly available documentation to justify the findings. However, it did not include the 236-page report submitted by language expert Toy Reid, who analyzed Chinese Communist Party dispatches between scientists at the Wuhan Institute of Virology (WIV) and their supervisors in Beijing. Katherine Eban of Vanity Fair and Jeff Kao of ProPublica were given advanced access to the Senate researchers’ documents and spent months conducting their own investigation. They interviewed Reid, talked with members Read More ›
Rats with Human Brains? The Real Story About Brain Organoids
Human brain organoids use adult stem cells from volunteer donors; they bypass the use of fetal tissue from abortionsIn Margaret Atwood’s MaddAddam Trilogy (2013) , the characters in the first book navigate a dystopian near-future with few ethical boundaries. Chicken has been genetically modified to be nothing more than meat and a mouth. For entertainment, they watch either pornography or televised executions. One of the central characters, the scientist who made the genetically engineered humans, ends up unleashing a synthetic pathogen intended to rid the world of evil. The excesses are reminiscent of Earth as described in the Flood narrative in the Bible (“Now the earth was corrupt in God’s sight and was full of violence.” Genesis 6:11). As in the Biblical account, a “flood” occurs when the synthetic pathogen ends up killing most of humanity. The remaining Read More ›

China’s Covid Theater: It’s Not Really About the Disease
Not exactly. As the Twentieth National Congress looms, the Chinese Communist Party does not want any COVID in BeijingThe Chinese Communist Party’s zero-Covid policy, heralded by Xi Jinping, is killing China’s economy and sinking citizens’ morale. Zero-Covid is viewed as a litmus test for support for the Communist Party, and Xi Jinping in particular. The goal is not saving lives but ensuring that the virus does not spread to Beijing ahead of the twentieth National Congress on October 16. Some hope that restrictions will ease after the National Congress. Others are less optimistic. The CCP under Xi Jinping declared “war on the virus” two years ago but the casualties in the Party’s pathogenic war have been the Chinese people. In the lead-up to the Twentieth National Congress in which Xi Jinping will announce his third term as General Read More ›
What Difference Has the CHIPS Act Made to the U.S. and Taiwan?
We need to first look at the broader picture of what the CHIPS Act is intended to doIn a previous article, I discussed the semiconductor industry and Taiwan’s supremacy in manufacturing microchips, the foundry portion of the semiconductor supply chain. Now let’s look at the U.S. perspective on the semiconductor industry and its relationship to Taiwan. In order to do that, we have to talk about the CHIPS+ Act Congress passed a bipartisan bill, the CHIPS and Science Act in July, after a year of negotiations in committee. President Biden signed the act into law on August 9 and the CHIPS Act Implementation Strategy was launched on September 6 through an executive order. CHIPS, or “Creating Helpful Incentives to Produce Semiconductors,” is a $250B initiative that incentivizes businesses to bring semiconductor manufacturing, research and innovation back to Read More ›
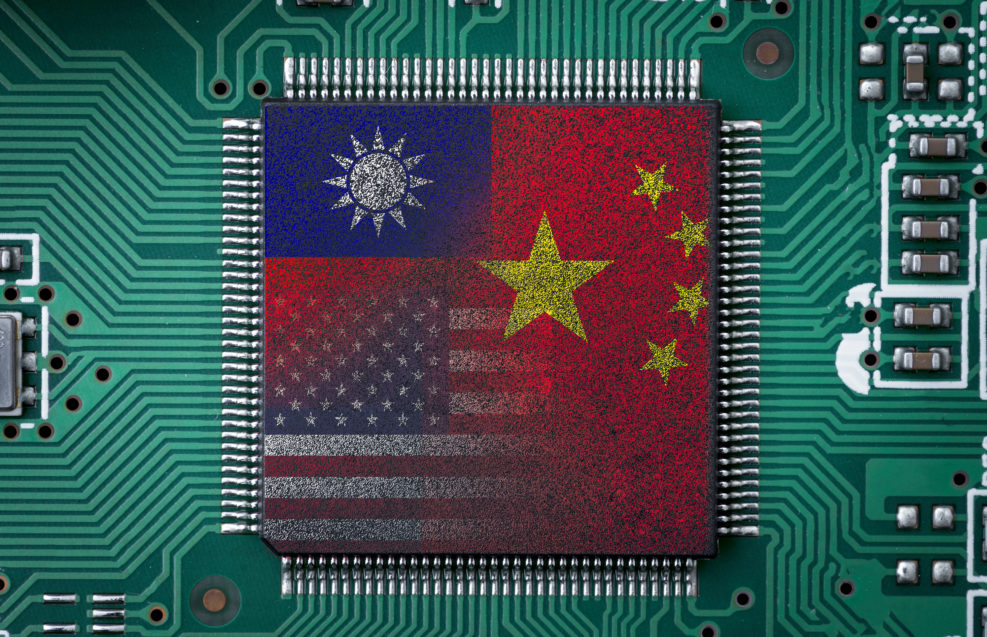
Taiwan Has Bet Its Uncertain Future on Advanced Microchips
An increasingly belligerent China has long claimed to own Taiwan, which manufactures 90% of the world’s *advanced* microchipsTaiwan is the world’s largest manufacturer of microchips*, and not just by a small margin. Taiwan manufactures 65% of the microchips used in everything from smartphones to missiles. This compares to the U.S. at 10% and China at 5%. South Korea and Japan produce the rest. More important, Taiwan manufactures 90% of the world’s advanced microchips. In other words, without Taiwan, the world’s supply of microchips would come to a standstill, something that has been keenly felt since 2021 when chip shortages affected the auto industry. So far, the world’s dependence on Taiwan’s chips has protected the self-governing island nation from a potential invasion or ruinous trade sanctions from China. Earlier, we looked at U.S. House Speaker Nancy Pelosi’s visit Read More ›

Pelosi’s Visit to Taiwan Matters to China. And to Your Computer
China staged an impressive display of military firepower at U.S, lawmaker Nancy Pelosi’s visit Taiwan — prominent in the globally crucial semiconductor “chips” industryU.S. House Speaker Nancy Pelosi’s visit to Taiwan at the beginning of August included a meeting with Mark Liu, head of the Taiwan Manufacturing Semiconductor Corporation (TMSC), which is the world’s largest producer of computer microchips — and makes most of the world’s advanced ones. Plans for Pelosi’s visit were first reported in Financial Times, after the trip was rescheduled due to COVID. China responded to the announcement with a global propaganda to present the visit as an act of defiance against the U.S. One China Policy. The U.S. One-China Policy recognizes the People’s Republic of China as the sole legal government of China but it does not necessarily agree with the PRC on Taiwan being a part of China. Read More ›

How China’s Pre-Crime Algorithms Work — and Their Fatal Flaw
The algorithms target, for example, those who complain about or draw attention to social injustices and abusesIn a previous article, we looked at the way George Orwell ’s dystopian 1984 is looking less and less like fiction as the Chinese Communist Party exploits the capabilities of AI and Big Data to surveil its entire population. But beyond surveilling citizens’ movements in real time, the CCP also hopes to predict crimes and protests before they happen. In a follow-up story in the New York Times, Paul Mozur, Muyi Xiao, and John Lui look at how the CCP is also bringing the dystopian world of Philip K. Dick ’s Minority Report (2002) to real life, with one difference: Rather than human “precogs” who can predict the future, the CCP relies on algorithms that can interrogate large swaths of Read More ›
