Forget Your Password? Apple Wants To End Them for Good But…
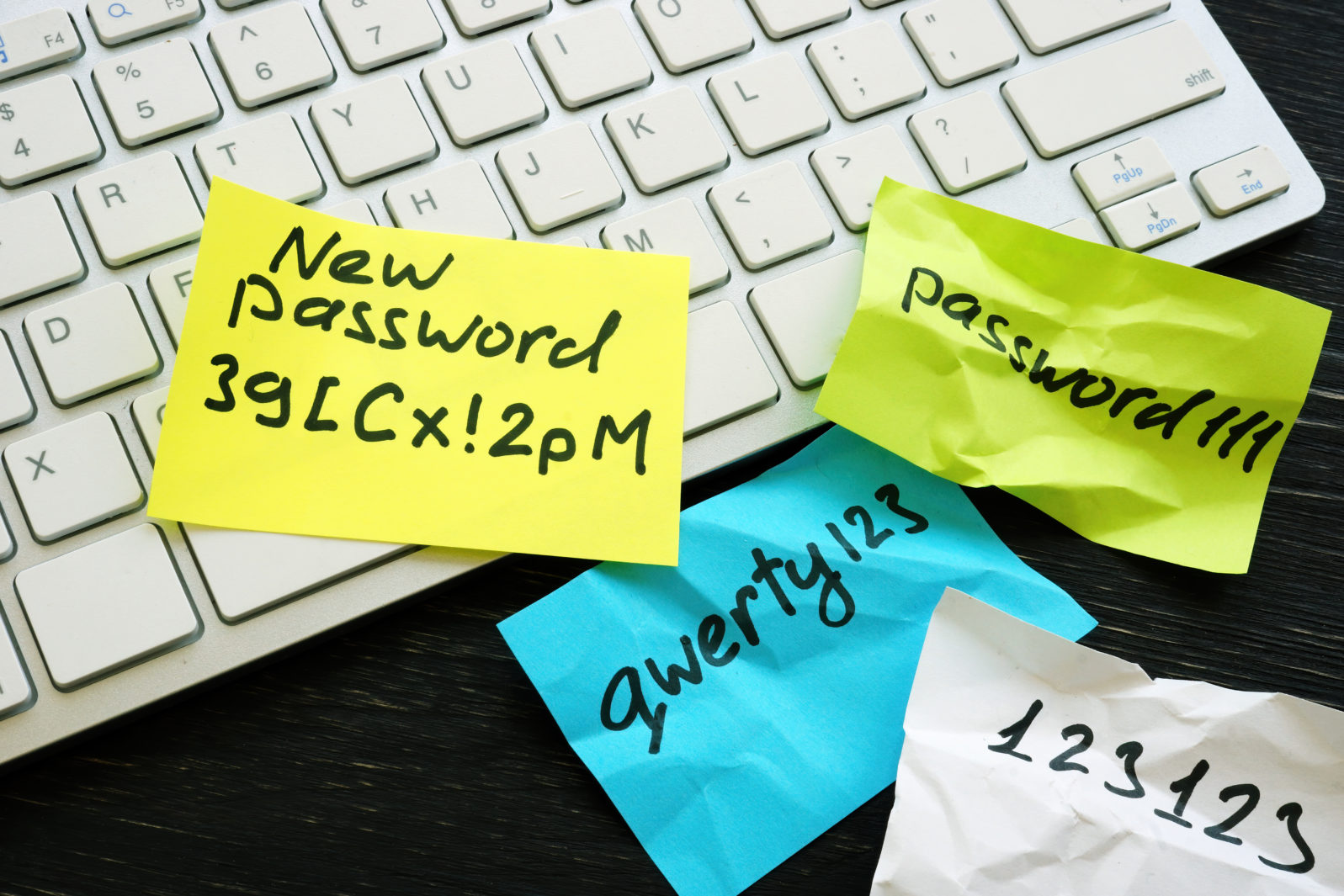
Do you want to give Apple your face- and fingerprints, maybe other “biometrics” down the road…?We’ve all heard the tales of woe about people whose password was “password” or “123456” or “BertJones”.
Currently, Big Tech, tired of the flak and the fallout, is trying to end passwords. Here’s Apple’s approach:
When Apple’s latest software updates for iPhones, iPads and Macs arrive this fall, they will include a way for users to log into various online accounts without entering passwords or relying on password managers to save and fill in credentials. The technology generates unique passkeys for each app or browser-based service in the place of characters. Those passkeys, a new type of identity authentication, prompt a scan of your face or fingerprints to log you in…
Passkeys, like those from Apple, are made up of a pair of related keys. One of the keys is public and sits on the service provider’s servers. The other is private and can’t be removed from your device. To log into an account, Apple will connect the two keys on the back end, and you will authenticate on the front end with Face ID or Touch ID. What users will see is a single-step option to get into their accounts.
If you’re signing in to a service for the first time, instead of designating a password, you will scan your biometrics on your Apple device. If you’re using an iPad or Mac, Touch ID will authenticate you. If you’re using an iPhone, Face ID will do the trick.
Dalvin Brown, “Apple Wants to End Passwords for Everything. Here’s How It Would Work.” at Wall Street Journal (June 12, 2022)

Microsoft and Google are also trying to get rid of the password. A more familiar approach for most of us has been authentication by sending a temporary password to another personal device, on the assumption that, if you got the e-mail or text message, it really is you. However, it might not be you, just someone who has gained control of more than one of your devices. So biometrics (a record of your unique physical characteristics) is emerging as the industry’s favorite option. But not without discomfort, if not pushback:
Actually killing the password entirely is a tricky, complicated prospect, given that they’ve been the de facto way of verifying your identity on the internet for decades, and many people will be loath to give up the comfortable and familiar method of logging in. Still, having the big browsers on board with this new method is a huge step. May we never have to type out nAsC4rr0xx420! ever again.
Boone Ashworth, “Apple, Google, and Microsoft Team Up to Vanquish the Password” at Wired (May7, 2022)
But wait. Could there be worse things in life than typing out “nAsC4rr0xx420!”?
So Apple has your face- and fingerprints. What if Apple soon wants a scan of your retina?:
“Retina scanning is a biometric verification technology that uses an image of an individual’s retinal blood vessel pattern as a unique identifying trait for access to secure installations.” – TechTarget, (December 2014).
“A retina scan is exactly what it sounds like: a machine that looks below your iris to scan the retina at the base of your eyeball. Since each person’s retina is unique, the scan offers security akin to a fingerprint — only retinas cannot be copied. The scanner emits a low-level beam of light to illuminate the back of eye while the user looks into a small eyepiece for about 30 seconds.” – Andrew Aarons, Chron.
“A biometrics retina scanner is one of the simplest biometric scanner devices that you can use in your office. The need for retina scanning and iris identification is rapidly increasing.” – Vincent Dail, Biometric-Security-Devices.com
It may come down to how much we trust that a Big Tech company will only use the information for virtuous purposes — as we individually understand the term “virtuous.”
Computer security expert David Kruger told Mind Matters News that we need to distinguish proposals to get rid of passwords in terms of who will gain more control as a result:

Getting rid of passwords is potentially a very good thing—but as always, the devil is in the details.
The phrase in the article “Apple will connect the two keys on the back end” fairly leaps off the page. If that sentence is correct, Apple’s architecture enables them to access both the user’s public and private keys—which means Apple has access to the all the content secured with those keys. Not good.
Referring to Absio Corporation’s work in this area (he is a vice-president), he notes,
Absio technology enables the user’s application, not Absio Corporation, to generate and manage public and private keys in a manner where we never ever have access to unencrypted copies of private keys.
Stay tuned. Stay cautious.
Note: You may also wish to look at: The true cause of cybersecurity failure and how to fix it. Hint: The cause and fix are not what you think. The problem has to do with the money Big Tech makes selling your information. David A. Kruger, a member of the Forbes Technology Council, says it’s getting worse: We’re in a hole so stop digging! Get back to root cause analysis.